North Korea-linked hack hits software that powers online services
North Korea-Linked Hack Hits Software That Powers Online Services
The digital landscape is currently facing one of its most sophisticated threats to date. Recent intelligence reports and cybersecurity audits have confirmed that a major North Korea-linked hack hits software that powers online services, sending shockwaves through the global tech industry. This isn't just a localized breach; it is a meticulously planned supply chain attack designed to infiltrate the very backbone of modern internet infrastructure.
As we navigate an era where cloud computing and automated software updates are the norm, the vulnerability of "trusted" software has become a primary target for state-sponsored threat actors. The Democratic People's Republic of Korea (DPRK), long suspected of utilizing cyber espionage to bypass international sanctions, has reportedly escalated its operations. This latest incident targets enterprise-level software tools that thousands of companies rely on to maintain their online presence, manage customer data, and facilitate digital transactions.
The Anatomy of the Attack: How State-Sponsored Hackers Compromised Critical Infrastructure
Imagine a typical Tuesday morning for Alex, a senior DevOps engineer at a mid-sized fintech firm. While sipping his coffee, Alex notices a slight anomaly in the server logs—a series of outbound connections to an unrecognized IP address. It looks like a standard background process, but something feels off. Upon further investigation, Alex realizes his team didn't authorize this traffic. He has just stumbled upon a "backdoor" hidden inside a routine software update for a network management tool his company has used for years.
This scenario is playing out in real-time across hundreds of organizations. The North Korea-linked hack hits software that powers online services by leveraging "trojanized" installers. Instead of attacking a company's firewall directly, the hackers compromised the software vendor's build environment. By injecting malicious code into a legitimate software update, they ensured that the malware was digitally signed and "trusted" by the target's operating system.
Key technical aspects of this breach include:
- Malicious DLL Side-Loading: The attackers used legitimate executable files to load a malicious Dynamic Link Library (DLL), effectively hiding their presence from traditional antivirus software.
- Multi-Stage Payloads: The initial infection was merely a "scout." Once inside a network, the malware would communicate with a Command and Control (C2) server to download more potent tools for data exfiltration.
- Stealthy Persistence: The code was designed to remain dormant for weeks, avoiding detection until a specific "trigger" was sent by the hackers.
- Exploitation of Zero-Day Vulnerabilities: In some instances, the threat actors utilized previously unknown flaws in web server configurations to gain initial access.
Cybersecurity firms like Mandiant and CrowdStrike have linked these tactics to the infamous Lazarus Group and Andariel—units believed to operate under North Korea's Reconnaissance General Bureau. These groups have moved beyond simple cryptocurrency theft; they are now targeting the very "plumbing" of the internet.
Why Supply Chain Attacks Are the New Frontier for State-Sponsored Hackers
The reason this North Korea-linked hack hits software that powers online services so effectively is rooted in the "one-to-many" advantage. In a traditional cyberattack, a hacker must breach one company at a time. In a supply chain attack, they only need to breach one vendor to gain access to that vendor's entire customer base. It is the digital equivalent of poisoning a city's water reservoir rather than individual wells.
This strategy is particularly devastating for online services. When the software providing load balancing, database management, or customer support interfaces is compromised, the downstream impact is astronomical. We are seeing a shift in the DPRK's tactical objectives. While financial gain through Ransomware-as-a-Service (RaaS) remains a priority, the acquisition of sensitive data and the ability to disrupt foreign infrastructure are becoming equally important goals.
The LSI keywords surrounding this event—such as "cyber espionage," "persistent threat actors," and "software integrity"—highlight a growing anxiety among IT leaders. The trust model that the software industry is built upon is under siege. When a developer downloads an NPM package or a sysadmin installs a patch from a reputable vendor, they are implicitly trusting thousands of lines of code they didn't write. The North Korean hackers have figured out how to exploit this trust with surgical precision.
Consider the broader implications for the global economy. If online services—ranging from e-commerce platforms to government portals—cannot guarantee the integrity of their underlying software, the digital economy slows down. The cost of remediation, including forensic audits, legal fees, and lost consumer trust, often exceeds the direct financial loss of the hack itself.
Global Response and the Escalating Threat of North Korean Cyber Espionage
In response to the news that a North Korea-linked hack hits software that powers online services, international intelligence agencies have issued urgent advisories. The FBI, CISA, and the UK's National Cyber Security Centre (NCSC) have published a joint report detailing the "Indicators of Compromise" (IoCs) associated with this campaign. This collective defense is necessary because the threat actors are incredibly resilient.
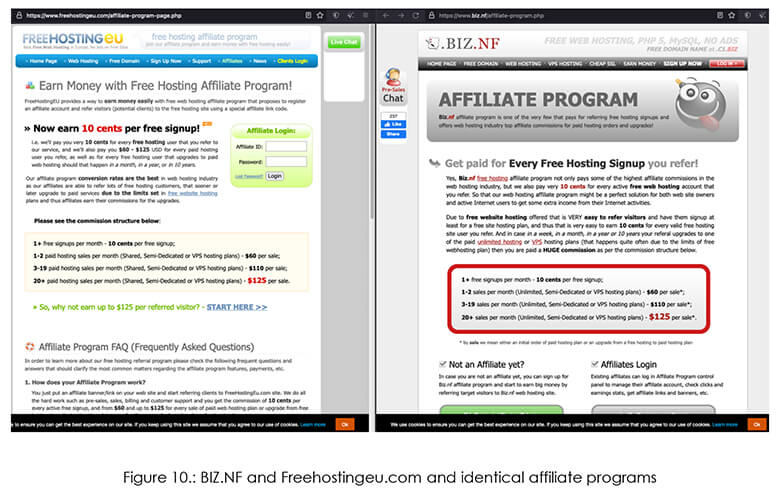
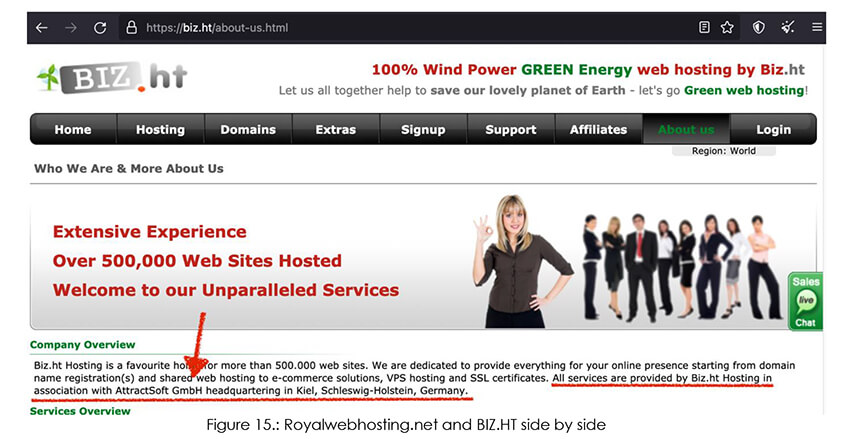
The North Korean regime uses these cyber operations as a vital source of hard currency and intelligence. Unlike other nations that might use hacking purely for geopolitical leverage, North Korea's "Bureau 121" operates like a corporate-military hybrid. Their hackers are often stationed abroad, using front companies to disguise their activities. They are known for their patience, often spending months researching a target's internal hierarchy and software stack before making a move.
Recent investigations have revealed that these hackers are also targeting:
- Managed Service Providers (MSPs): By hitting companies that manage IT for others, they gain a "God-view" of multiple client networks.
- Cloud Service Providers: Exploiting misconfigured S3 buckets and cloud permissions to move laterally through virtual environments.
- Critical Infrastructure: Testing the waters for potential disruptions to power grids and water treatment facilities.
- Cryptocurrency Exchanges: Continuing their streak of high-value heists to fund the nation's weapons programs.
The storytelling of modern warfare has moved from the battlefield to the keyboard. The "invisible war" is being fought in the lines of code that power our social media, our banking apps, and our healthcare systems. The fact that a North Korea-linked hack hits software that powers online services is a wake-up call that geographical borders offer no protection against digital incursions.
Lessons for Enterprises: Protecting Your Online Services from Sophisticated Intruders
As the "North Korea-linked hack hits software that powers online services" headline continues to dominate tech news, business leaders are asking: "Are we next?" The reality is that no organization is 100% unhackable. However, the difference between a minor incident and a catastrophic breach lies in preparation and a "Zero Trust" architecture.
To defend against state-sponsored actors who specialize in software supply chain compromises, organizations must evolve their defensive posture. It is no longer enough to have a strong perimeter; you must assume that the threat is already inside your network. This shift in mindset is crucial for the long-term survival of any online service provider.
Here are the strategic steps enterprises should take immediately:
- Software Bill of Materials (SBOM): Maintain a detailed inventory of every software component, library, and third-party dependency used in your environment. This allows you to quickly identify if a compromised "ingredient" is part of your system.
- Endpoint Detection and Response (EDR): Deploy advanced tools that monitor process behavior in real-time, rather than just looking for known file signatures.
- Network Segmentation: Isolate critical online services from the rest of the corporate network. If a management tool is hacked, the attacker should not be able to hop over to the customer database.
- Strict Update Verification: Implement a staging environment where all software updates are "sandboxed" and monitored for suspicious outbound traffic before being pushed to production.
- Multi-Factor Authentication (MFA): While it won't stop a software-level hack, it prevents hackers from using stolen credentials to escalate their privileges once they are inside.
The North Korea-linked hack hits software that powers online services because it exploits the weakest link: human trust in automation. By integrating human oversight back into the update process and utilizing AI-driven threat hunting, companies can build a more resilient digital fortress. We are currently in a high-stakes game of cat and mouse, where the "cats" are nation-state hackers with infinite patience and the "mice" are the global services we use every day.
In conclusion, the news that a North Korea-linked hack hits software that powers online services is a stark reminder of our digital fragility. As we continue to move more of our lives and businesses online, the value of cybersecurity has never been higher. It is a continuous battle for integrity, requiring collaboration between governments, software vendors, and end-users. The hackers are evolving; the question is, are we evolving fast enough to stop them?
North Korea-linked hack hits software that powers online services
North Korea-linked hack hits software that powers online services Wallpapers
Collection of north korea-linked hack hits software that powers online services wallpapers for your desktop and mobile devices.

Amazing North Korea-linked Hack Hits Software That Powers Online Services Wallpaper Art
Discover an amazing north korea-linked hack hits software that powers online services background image, ideal for personalizing your devices with vibrant colors and intricate designs.

Detailed North Korea-linked Hack Hits Software That Powers Online Services View Digital Art
Explore this high-quality north korea-linked hack hits software that powers online services image, perfect for enhancing your desktop or mobile wallpaper.
Breathtaking North Korea-linked Hack Hits Software That Powers Online Services Background Art
Experience the crisp clarity of this stunning north korea-linked hack hits software that powers online services image, available in high resolution for all your screens.
Serene North Korea-linked Hack Hits Software That Powers Online Services Image Art
Explore this high-quality north korea-linked hack hits software that powers online services image, perfect for enhancing your desktop or mobile wallpaper.
Vivid North Korea-linked Hack Hits Software That Powers Online Services Design Photography
Transform your screen with this vivid north korea-linked hack hits software that powers online services artwork, a true masterpiece of digital design.

Dynamic North Korea-linked Hack Hits Software That Powers Online Services Photo for Desktop
Find inspiration with this unique north korea-linked hack hits software that powers online services illustration, crafted to provide a fresh look for your background.
Vivid North Korea-linked Hack Hits Software That Powers Online Services Image Illustration
Explore this high-quality north korea-linked hack hits software that powers online services image, perfect for enhancing your desktop or mobile wallpaper.

Artistic North Korea-linked Hack Hits Software That Powers Online Services Picture for Desktop
A captivating north korea-linked hack hits software that powers online services scene that brings tranquility and beauty to any device.

Detailed North Korea-linked Hack Hits Software That Powers Online Services View Concept
Explore this high-quality north korea-linked hack hits software that powers online services image, perfect for enhancing your desktop or mobile wallpaper.

Gorgeous North Korea-linked Hack Hits Software That Powers Online Services Background for Mobile
This gorgeous north korea-linked hack hits software that powers online services photo offers a breathtaking view, making it a perfect choice for your next wallpaper.

Gorgeous North Korea-linked Hack Hits Software That Powers Online Services Landscape Collection
Find inspiration with this unique north korea-linked hack hits software that powers online services illustration, crafted to provide a fresh look for your background.

Amazing North Korea-linked Hack Hits Software That Powers Online Services Abstract Art
Explore this high-quality north korea-linked hack hits software that powers online services image, perfect for enhancing your desktop or mobile wallpaper.

Breathtaking North Korea-linked Hack Hits Software That Powers Online Services Wallpaper in 4K
Discover an amazing north korea-linked hack hits software that powers online services background image, ideal for personalizing your devices with vibrant colors and intricate designs.

Exquisite North Korea-linked Hack Hits Software That Powers Online Services Scene for Your Screen
Find inspiration with this unique north korea-linked hack hits software that powers online services illustration, crafted to provide a fresh look for your background.

Vivid North Korea-linked Hack Hits Software That Powers Online Services Wallpaper Art
Experience the crisp clarity of this stunning north korea-linked hack hits software that powers online services image, available in high resolution for all your screens.

Gorgeous North Korea-linked Hack Hits Software That Powers Online Services Moment Art
This gorgeous north korea-linked hack hits software that powers online services photo offers a breathtaking view, making it a perfect choice for your next wallpaper.

Vibrant North Korea-linked Hack Hits Software That Powers Online Services Image Digital Art
Experience the crisp clarity of this stunning north korea-linked hack hits software that powers online services image, available in high resolution for all your screens.

Beautiful North Korea-linked Hack Hits Software That Powers Online Services Image Illustration
Transform your screen with this vivid north korea-linked hack hits software that powers online services artwork, a true masterpiece of digital design.

Artistic North Korea-linked Hack Hits Software That Powers Online Services Landscape for Your Screen
Find inspiration with this unique north korea-linked hack hits software that powers online services illustration, crafted to provide a fresh look for your background.

Vibrant North Korea-linked Hack Hits Software That Powers Online Services Image Concept
Explore this high-quality north korea-linked hack hits software that powers online services image, perfect for enhancing your desktop or mobile wallpaper.
Download these north korea-linked hack hits software that powers online services wallpapers for free and use them on your desktop or mobile devices.
0 Response to "North Korea-linked hack hits software that powers online services"
Post a Comment